Category Archives: Privacy
NSA: What’s Privacy Got to Do with It?
You must understand
That the touch of your wand
Makes my pulse react
That it's only the skill
Of breaking our will
Opposites attract
It's physical
Only logical
You must try to ignore
That it means more than that
[Chorus:]
NSA: What's privacy got to do, got to do with it?
What's privacy but a second hand emotion?
What's privacy got to do, got to do with it?
Who needs a code when the code can be broken?
It may seem to you
That I'm acting confused
When you're close to me
If I tend to look dazed
I've read it someplace
I've got cause to be
There's a name for it
There's a phrase that fits
But whatever the reason
You do it to me
[Chorus]
I've been taking on a new direction
But I have to say
I've been thinking about my own protection
It scares me to feel this way
[Chorus]
NSA: What's privacy got to do, got to do with it?
What's privacy but a sweet old fashioned notion?
What's privacy got to do, got to do with it?
Who needs a code when the code can be broken…
The Mobile Lawyer & Professional Responsibility: Friday in Long Beach

Just a quick reminder that I'm presenting Program #19 at the Calbar Solo and Small Firm Summit in Long Beach, California:
The Mobile
Lawyer & Professional Responsibility: Confidentiality in the Digital Age
Friday, June 21, 2013
1:15 p.m.-2:15 p.m.
Lawyers
are open for business 24-hours a day.
They communicate via Twitter & Facebook, on smartphones, tablets
& notebooks – in coffee shops, taxicabs, airports and on airplanes. This program reviews recent COPRAC opinions
addressing technology and provides tools to protect confidences and privacy for
both attorney and client.
It's not too late to register and join us!
eDiscovery 101: Required Reading on Metadata

The Guardian US interactive team has posted, “A Guardian guide to your metadata“; and for anyone who is still bewitched, bothered and bewildered by the concept, I urge them to take a look at this interactive demonstration.
What’s also interesting is that one of the examples they use is the Petraeus scandal, just like I did a few months ago. The reason it’s such an excellent learning tool is that individuals tend to worry about their own metadata, completely ignoring their risk of harm by others’ metadata.
Obviously, with the strange happenings at the NSA, this might be the perfect time to understand the world around us a little bit better.
Upcoming Presentation: Calbar Solo & Small Firm Summit: “The Mobile Lawyer & Professional Responsibility: Confidentiality in the Digital Age”
I didn't intend for this blog to be a billboard for all of my 'stuff', but lacking much time these days, that's what it's been lately. Since I'm already on a roll, I might as well tell you about a new program I'm presenting at the Calbar Solo and Small Firm Summit in Long Beach, California. The Summit runs from June 20 – 22, 2013 and my program (#19) is entitled:
The Mobile
Lawyer & Professional Responsibility: Confidentiality in the Digital Age
Friday, June 21, 2013
1:15 p.m.-2:15 p.m.
Lawyers
are open for business 24-hours a day.
They communicate via Twitter & Facebook, on smartphones, tablets
& notebooks – in coffee shops, taxicabs, airports and on airplanes. This program reviews recent COPRAC opinions
addressing technology and provides tools to protect confidences and privacy for
both attorney and client.
Hope to see you there!
Summary of Executive Counsel Exchange – Day One
Last week, I attended day one of the Executive Counsel Exchange in Los Angeles, as has been my custom the past three years. Just to clarify, this conference is sometimes referred to as the Executive Counsel 'Institute', but the actual program is called, "The Exchange" and the theme is, "e-Discovery
for the Corporate Market".
This year, the primary moderators were Browning Marean III of DLA Piper, my old pal Robert Brownstone of Fenwick & West and David Kessler of Fulbright & Jaworski. This is one of my favorite programs because it's a roundtable.
The reason this particular conference is so beneficial is that attendees share their day-to-day experiences confronting the many eDiscovery challenges we know so well. I've always considered the practical much more important than the theoretical – mostly because people, situations and budgets don't tend to comport to the (IMHO) wishful thinking that appears in many overly-optimistic project plans.
Take a look at the agenda. If these look like the kinds of issues you see, think about attending. The next event will be held in late March in San Francisco.
eDiscovery California: Social Media Laws Take Effect Jan. 1, 2013
 Welcome back, all. I hope you had a nice holiday and are fully rested so that you may now spend the rest of the season…at the mall! We're getting close to the New Year and as is true each time we approach January 1st, we have a bunch of new laws taking effect. California employers and post-secondary institutions should take note of two of them; AB 1844 and SB 1349. Both were signed into law by Gov. Jerry Brown back on September 27th, 2012.
Welcome back, all. I hope you had a nice holiday and are fully rested so that you may now spend the rest of the season…at the mall! We're getting close to the New Year and as is true each time we approach January 1st, we have a bunch of new laws taking effect. California employers and post-secondary institutions should take note of two of them; AB 1844 and SB 1349. Both were signed into law by Gov. Jerry Brown back on September 27th, 2012.
Although the language in each bill is different, essentially, AB 1844 prevents employers (also potential employers) from demanding, using or exploiting an employee's (or potential applicant's) social media passwords and information.
SB 1349 is substantially similar, except that it applies to post-secondary institutions; both public and private.
There is speculation in the media about the necessity of these types of regulations. Many believe that a substantial risk of invasion of privacy doesn't exist. Maybe not; but moving forward, I believe the risk will increase exponentially.
What's next – bionic mannequins???
eDiscovery 101: Petraeus was Done In by Gmail Metadata – Someone Else’s!
 I’m sure you all know by now that I don’t venture into scandals, per se, on this blog; except when they involve our area of examination: Technology, privacy, evidence and eDiscovery.
I’m sure you all know by now that I don’t venture into scandals, per se, on this blog; except when they involve our area of examination: Technology, privacy, evidence and eDiscovery.
That said, I’ve certainly been following the messy Patreaus developments, becoming more and more interested in the Gmail connection to all of it. None of the initial stories answered my question; if a woman was allegedly being harassed by Paula Broadwell, why did they need to monitor her (Broadwell’s) Gmail account, since the victim would be the recipient of all of the emails, and have them in her possession? It suggested to me – and probably to some of you – that the harassing emails were probably being sent anonymously and had to be traced back to the source to specifically identify who was behind them (Broadwell).
This morning, we received confirmation. Naturally, the situation is going from bad to worse faster than you can say, “October surprise”, but for our purposes, the interesting link is the metadata (specifically rich location-data) gleaned from the victim’s inbox, which provided the trail back to Broadwell by linking her physical whereabouts to the devices that were the sources of the emails; which ultimately led back to Petraeus through clandestine emails in Broadwell’s – not his – inbox.
Got all that? Good. And what are the things that bother me (I refuse to utter the oft-annoying “raises questions”)?
- What in the world is the Director of the CIA doing with a Gmail account?
- If any of these messages were sent via mobile technology, why didn’t the sender disable GPS monitoring (recall my recent post about location-privacy)?
- Apparently some of the correspondences between Broadwell and Petraeus were pretty racy. Did they really think it would remain private?
Considering both Petraeus and Broadwell apparently set up anonymous Gmail accounts specifically to facilitate carrying on their affair, it once again calls into question the very knowledge, training – and self-awareness – of those who we charge to protect this country and its secrets.
Simply put, if even Petraeus doesn’t get it, who the he** does???
Perry Segal Discusses the Cloud, Privacy & Attorney Ethics on KUCI Irvine 88.9FM – Monday, Nov. 12th at 8:00 a.m. PST
I guess the headline says it all, except I'd like to add that the interview will also be available as a podcast via iTunes. I will also post an MP3 here Monday.
Here's a few of the additional details:
Privacy Piracy (88.9FM and www.kuci.org), a half-hour public affairs show with no
commercials broadcasts from the University of California, Irvine campus on
Mondays from 8:00 a.m. – 8:30 a.m. Pacific Time. To learn more
about the show and listen to archived interviews, please visit www.kuci.org/privacypiracy.
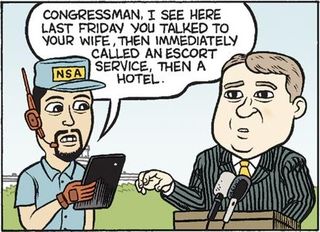
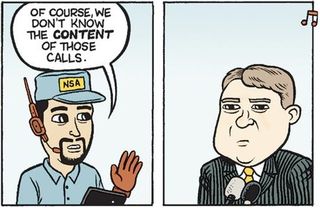
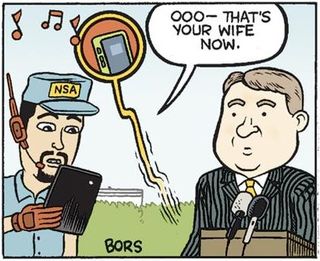
We are Not Alone
 A lot of people may not agree with me, but I stand behind this simple advice; assume you are being watched/followed/transcribed/recorded 24 hours a day, seven days a week.
A lot of people may not agree with me, but I stand behind this simple advice; assume you are being watched/followed/transcribed/recorded 24 hours a day, seven days a week.
Act accordingly. Of course, the key is in balancing confidentiality without venturing over the line into paranoia. I can’t help you, there. It comes down to using your best judgment.
Or, you can do what Patrick Moran, the son of Congressman Jim Moran, did…